Drone Swarm: A Complete Defensive Guide

For decades, security was about protecting high-value assets with even higher-value interceptors. But the “New Reality” of drone swarms has flipped the script because a single, off-the-shelf drone can now threaten multi-million dollar infrastructure, forcing a defender to choose between catastrophic damage or depleting expensive stockpiles. What was once a singular UAV incursion is increasingly a coordinated, multi-vector swarm, with multiple platforms converging from diverse bearings and altitudes to saturate sensors, compress decision timelines, and exhaust interceptors.
With the global UAV market projected to reach $21.81 billion by 2030, increasing drone traffic and shrinking verification timelines are driving demand for automated cueing, correlation, and prioritization, while keeping human decision authority where required.
For security decision-makers focused on mission continuity, relying on isolated sensors is no longer sufficient. You need an automated, open-architecture system that can verify and neutralize drone swarms before they reach your perimeter.
What is a Drone Swarm?
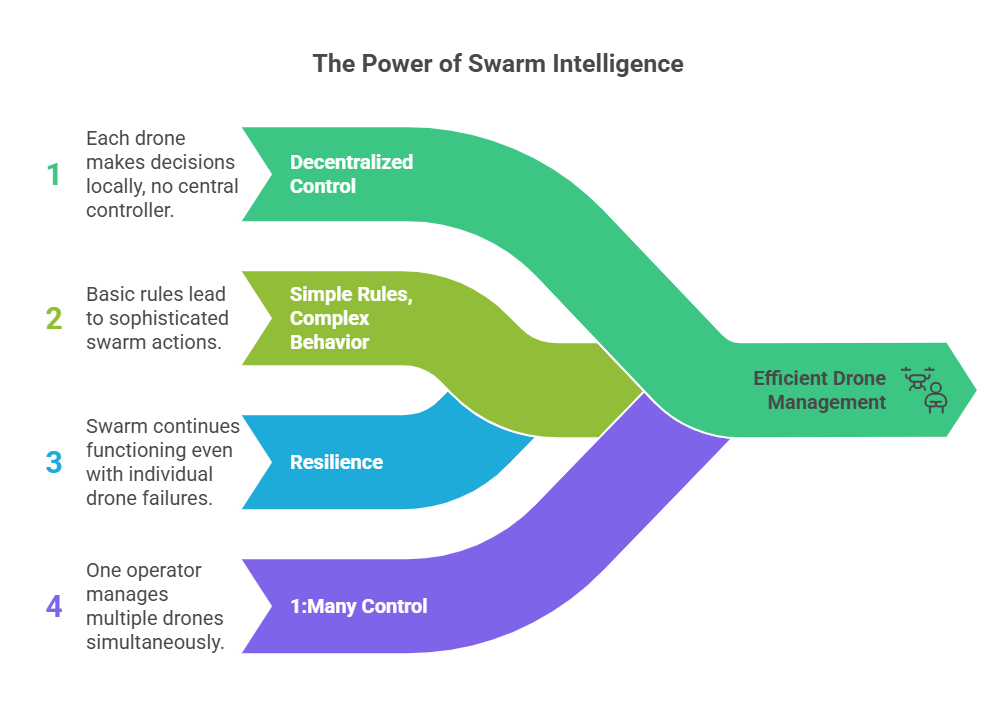
A drone swarm is a coordinated group of UAVs that functions as a unified system, using onboard autonomy to share tasks and adapt in real time. Coordination is often distributed. Each drone responds to local sensor inputs and nearby peers, with a mission-level controller sometimes providing overarching goals and constraints.
This “distributed intelligence” enhances scalability and resilience, shifting the human role from continuous manual control to high-level supervision of mission outcomes.
In practice, swarms are characterized by:
- Distributed coordination: no single point of failure; drones continue operating even if some nodes are lost.
- Simple rules, complex behavior: local interactions enable coordinated formations, adaptive search patterns, and dynamic task allocation.
- Resilience: the swarm can re-route, re-form, or reassign tasks dynamically in response to changing conditions.
This shift from 1:1 control to 1:many supervision enables a small team, or even a single operator, to manage dozens of UAVs, depending on autonomy level, mission complexity, and communications reliability.
The Three Pillars of Swarm Threats
- Resilience. Swarms are designed for attrition, with no single point of failure. Using decentralized autonomy, remaining drones can continue operating and redistribute tasks if nodes are lost.
- Saturation. Swarms create “target saturation,” overwhelming defenders’ radar and processing systems with too many data points to be tracked or engaged effectively.
- Cost Asymmetry. Swarms can be composed of “off-the-shelf” drones costing a fraction of traditional defence systems and interceptors.
How Swarms Overwhelm Traditional Systems
Drone swarms are effective because they exploit both the technical and cognitive limitations of existing security infrastructure. Traditional 3D radars (measuring range, azimuth, and elevation) are often optimized for higher-altitude, higher-RCS targets. Low, slow, small drones can be difficult to detect and track, especially at low altitude or in cluttered environments, without specialized counter-UAS waveforms and processing. Recent drone warfare has accelerated the shift from isolated incidents to mass, time-compressed swarm threats, overwhelming conventional defenses.
The true danger of a swarm is that it can present as a single, massive, confusing cluster to legacy detection systems. Because drones are small, slow, and typically fly low, many radars use thresholds and tracking logic to filter out what appears to be clutter. This trade-off can reduce sensitivity to small, slow targets and increase the risk of missed detections or delayed tracking in complex environments.
Standard counter-drone systems rely on Electronic Warfare (EW) to disrupt control links and/or navigation aids where authorised. However, drones with higher autonomy can operate with minimal radio-frequency (RF) command links, reducing the effectiveness of RF-only defeat methods. Many UAS still emit detectable RF or rely on GNSS and other navigation aids, but guidance and emissions profiles vary widely. As a result, effective defense typically requires layered sensing and multiple mitigation strategies, tailored to rules of engagement, legal authorities, and the operational environment.
In a manual security setup, a human operator must identify a threat, verify it, and respond to each threat individually. A swarm of 50+ drones creates a “Data Flood,” overwhelming operators with simultaneous targets. Without C4I automation, this forces personnel to cycle through cameras and engage threats one by one, resulting in critical delays and reduced effectiveness.
Here’s how to defend against drone swarms.
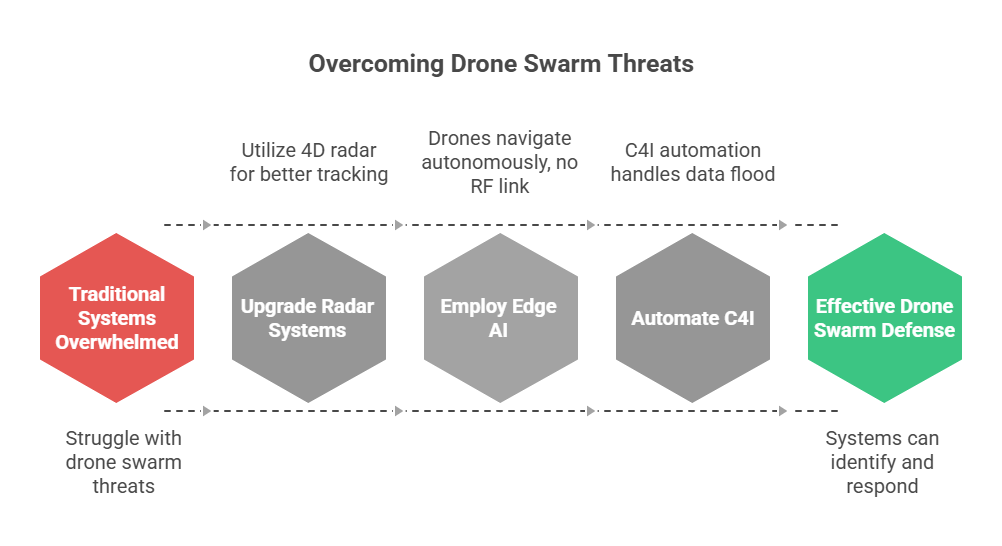
Phase 1: Advanced Detection & The Multi-Sensor Mosaic
Newer counter-UAS radars (often referred to as 4D radars) deliver faster update rates and advanced Doppler processing, enabling improved detection, tracking, and classification of low-altitude targets in cluttered environments. While 4D radar excels at tracking the physical movement and velocity of drone swarms, it is most effective when integrated with RF intelligence and acoustic sensors. These additional layers help identify drones engineered to be “low-observable” or signal-silent. Acoustic sensors, in particular, can fill critical gaps by detecting RF-silent drones at close range, though their effectiveness can be limited by ambient noise, weather conditions, and local terrain clutter.
SKYLOCK can integrate 4D radar, RF intelligence, and AI-assisted optical sensors (configuration-dependent) to provide long-range, volumetric tracking and cueing for drone-swarm detection and verification. This processing can improve discrimination between drones and birds (e.g., via Doppler/micro-Doppler features), supporting long-range detection, with effective range dependent on sensor configuration, target profile, terrain/clutter, spectrum conditions, and local operating constraints. This preserves decision time for verification and response when swarms compress timelines.
Once a potential threat is flagged by radar or RF, Electro-Optical (EO) and Infrared (IR) cameras provide the final visual confirmation. In high-clutter environments (such as airports or cities), AI algorithms can analyze flight patterns and physical characteristics to differentiate between birds and drones. IR sensors detect the thermal signatures of drone batteries and motors, supporting night operations. However, sensor performance may degrade in obscurants and adverse weather such as fog, heavy rain, or high humidity.
Phase 2: The “Kill Chain” – Proportional Response Options
In Phase 2, the “Kill Chain” moves from detection to neutralisation. The objective is to deliver a proportional response, stopping the threat with the least disruptive method available while maximizing the probability of intercept and ensuring compliance with rules of engagement (ROE) and legal authorities.
Soft-Kill: Broad-Spectrum Mitigation
Soft-kill methods focus on disrupting the “brain” or “ears” without physically destroying it.
RF jamming and spoofing are often the first line of defence where authorised. Area-denial jamming saturates control and telemetry bands with noise (where authorised), severing the command link between drone and pilot. Navigation interference, including spoofing (where authorised), can more precisely target navigation systems than broadband jamming, but effectiveness depends on the drone’s guidance architecture, anti-spoofing resilience, and the operational environment.
Hard-Kill: Precision Kinetic Disruption
When soft-kill fails, the system must physically remove the threat from the sky. Drone-on-drone interceptors, guided by AI vision, engage targets through kinetic collisions (ramming) or by deploying nets. These non-explosive hard-kill options can reduce collateral risk compared to traditional explosive interceptors, making them suitable in environments with strict safety requirements.
For high-speed or high-volume swarm threats, directed-energy weapons such as lasers provide a virtually unlimited magazine, constrained mainly by power supply, thermal management, and safety protocols. This makes them effective when facing large numbers of simultaneous targets.
In sensitive areas like airports or stadiums, non-explosive intercept options, like net capture or other disable mechanisms (where authorised), may be preferred to minimize collateral risk. Suitability depends on site-specific safety constraints, engagement geometry, and operational regulations.
Phase 3: Strategic Command – C4I and Integration
Phase 3 is where the swarm’s “data flood” is distilled into actionable intelligence for rapid decision-making. Without a central C4I (Command, Control, Communications, Computers, and Intelligence) system, sensor feeds remain fragmented, slowing verification and response.
A modern C4I platform, such as SKYLOCK’s integrated software, serves as the central nervous system for drone defence. Instead of having a separate monitor for radar, another for cameras, and a third for jammers. This “mosaic” approach means, where available, you can plug in a 4D radar from one company and a high-power laser from another. The “Brain” automatically translates their different languages into a single, unified map of the battlespace.
The C4I software uses AI-driven filtering. For autonomous triage, the system automatically categorises targets by threat level. The software can automate correlation, prioritisation, and operator workflows (e.g., cueing, tracking, and tasking), while engagement decisions remain aligned to ROE and operator authority.
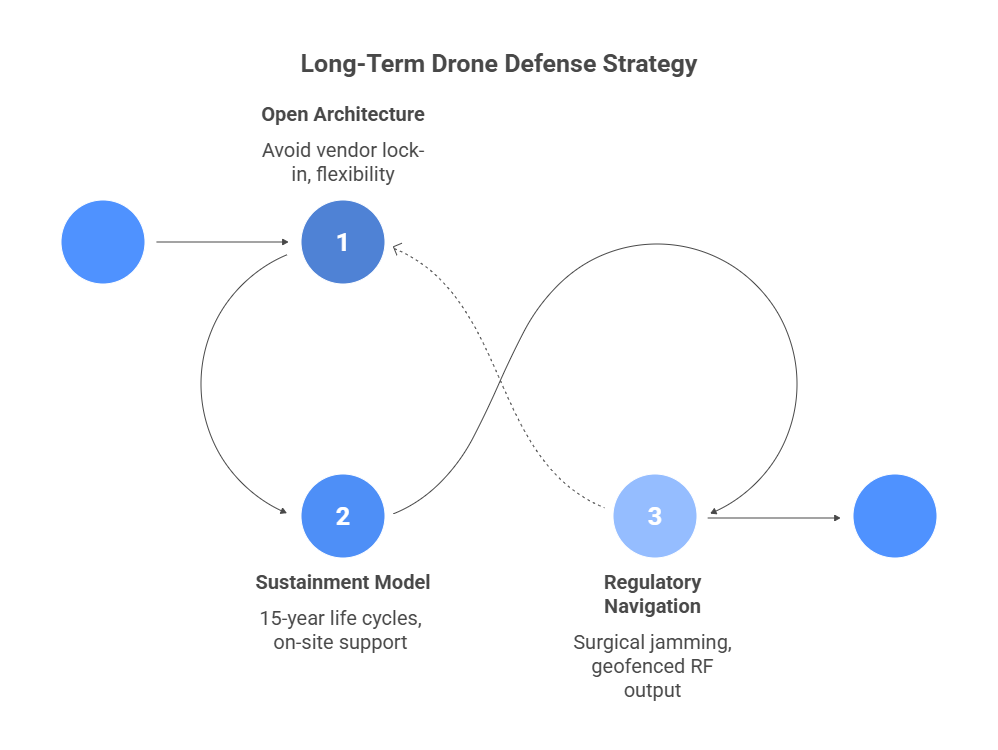
Long-Term Defence Strategy with Procurement and Sustainment
A Long-Term defence Strategy focuses on ensuring the technology doesn’t become obsolete or a financial burden. Here are the three major factors to consider.
1. Avoiding Vendor Lock-In: The Power of Open Architecture
“Vendor Lock-In” occurs when a company builds a “closed” system in which its radar only works with its specific jammer. By choosing Open-Architecture systems, you maintain “buyer power.” You can swap out an older 3D radar for a newer 4D model from a different manufacturer without rebuilding the entire command centre. From a cybersecurity standpoint, aligning governance and access controls with frameworks like ISO/IEC 27001 (and its Annex A control set) helps reduce integration risk as systems evolve.
Open systems allow you to “plug in” new software patches or specialized sensors (like acoustic detectors) via standardized APIs as soon as they hit the market, keeping you ahead of rapidly advancing drone swarms.
2. The Sustainment Model: 15-Year Life Cycles
Drone defence is now part of Critical National Infrastructure. You cannot afford “downtime” because a spare part is backordered. Configurable sustainment packages are customized service agreements that place “forward-deployed” spare parts and technicians directly on-site or in-region. With the right spares strategy and SLA, some failures (e.g., cooling subsystems) can be addressed quickly, reducing downtime compared to backordered repair cycles.
National security ecosystems require longevity. A long-term SLA can define commitments for software updates, cybersecurity patches, and hardware maintenance for the actual lifespan of the base or airport, providing “budgetary certainty” for government planners. Once you’ve built the brain, protecting the C2 layer becomes part of mission readiness.
3. Regulatory Navigation: The Legal Minefield
Technological capability often moves faster than the law. Navigating the Legal Landscape is as important as the hardware itself. In regions like North America, the FCC and FAA have strict rules against jamming because it can interfere with commercial aircraft or cell towers. Strategy here focuses on “surgical” jamming or “kinetic” (physical) intercepts that don’t mess with the radio spectrum.
In countries like Thailand or India, regulations are shifting rapidly to allow for “Drone Zones.” A long-term strategy involves working with local regulators to ensure the system’s RF output is “geofenced,” meaning the jammer only activates in a specific 3D box of airspace, protecting the public while securing the target.
Beyond the “Kill” is Building A defence Legacy
Defending against a swarm is about ensuring that your defence system doesn’t become a financial burden or technically obsolete within three years. Because drone technology evolves rapidly, a “closed” proprietary system is actually your greatest vulnerability. SKYLOCK’s in-house development philosophy is designed to solve this, providing an open-architecture “brain” that lets you plug in new 4D radars, acoustic sensors, or AI software patches as the threat landscape shifts.
By integrating vertical height and velocity tracking with lower-collateral-risk hard-kill options like the Sky-Interceptor, SKYLOCK provides a path to operational assurance even in dense urban environments or sensitive areas like airports. We don’t just sell hardware; we provide 15-year sustainment models and customized service agreements to ensure your critical infrastructure remains secure for the long haul.
Ready to stress-test your current airspace security? Talk to our defense expert today to discuss a bespoke, geofenced defense strategy for your needs.



